What Happens When AI has Read Everything
The AI systems have read, analyzed, and digested the entire collective knowledge of humanity. What happens when AI has read everything?

(How to Hack Instagram). With over 300 million active users and growing daily, Instagram has become one of the world's most popular social media sites.
Instagram is one of the free, most popular photo-sharing social media platforms. Instagram lets you share your photos and videos with your friends and family. But what if you get hacked? Like other popular social media platforms, cybercriminals always look to break into an Instagram account.
It will cover the five most common methods of hacking Instagram accounts and how you can avoid them.
Table of contents [Show]

One of the most common ways people can hack into your Instagram account is through a brute force attack. This is where someone uses a computer program to systematically generate guesses of possible passwords until they find the right one. Many of these programs can guess thousands or even millions of possible passwords per second.
To make things more difficult for hackers, use eight characters or more in your password and mix in numbers, letters, and special symbols if possible.

On your computer, malicious programs can be installed that would be able to monitor and control everything you do on your device. The malware may start from a rogue Wi-Fi network or infect an unsecured website, but you are never safe while online.
Remote keyloggers will have access to everything that is typed in at the keyboard, and because of this, users should always make sure they have antivirus protection on their computers. They work using software such as Dragon Naturally Speaking, which has speech recognition capabilities.
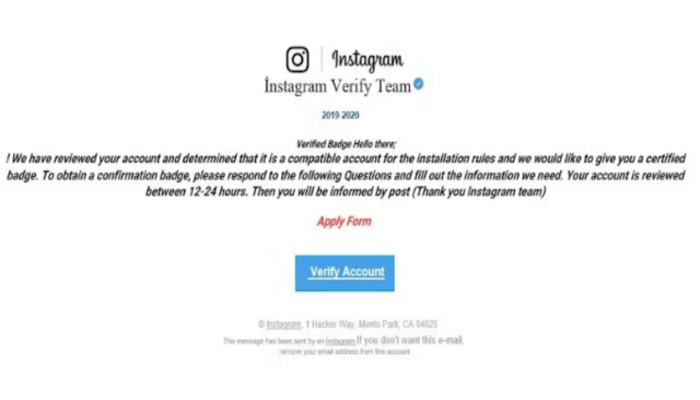
Phishing emails are a common way for hackers to collect personal information and take over someone's account. Phishing emails often look just like real emails from a company and ask for the user's login information. To avoid getting hacked, you should always be careful with whom you share your private information, especially when clicking on suspicious links or attachments.

A solid grasp of the latest vulnerabilities will help you avoid getting hacked. We've found that the most common zero-day vulnerabilities lie in third-party software. It is always a good idea to have your company's IT administrator perform periodic software updates, especially if developers announce significant new updates or releases.
In the case of third-party applications, social media marketing platforms like Hootsuite and Gmail could also leave their clients vulnerable if they don't keep up with their security updates.

Mobile OS vulnerabilities are a leading cause of mobile hacks. As sisters, app makers must watch for OS vulnerabilities when installing or creating apps. Find any recently updated security patches on your phone (typically found in the Settings app). Contact your device's manufacturer for more information if you don't see any recent updates.
While there are many ways that you can protect yourself against these threats, the best defense is still a potent offense. Stay vigilant, keep updated on the latest risks, and ensure your password has at least twelve characters, including upper-case letters, lower-case letters, numbers, and symbols.
Zphisher is a powerful open-source tool for Phishing devices. It has become very famous for phishing assaults on the right track. Zphisher is easier than Social Engineering Toolkit. It consists of some templates generated by a tool known as Zphisher.
It gives phishing templates for webpages for 18 popular websites, which include Facebook, Instagram, Google, Snapchat, GitHub, Yahoo, Proton mail, Spotify, Netflix, LinkedIn, WordPress, origin, Steam, Microsoft, and so forth.
1. Check login interest.
2. Verify your cellphone number and electronic mail within the settings.
3. Search for new log notifications in your email.
4. Have a study of your feed and memories.
5. Open your Instagram direct messages.
6. Evaluate questionable remarks.
7. Look at your email and cope with signs of hacking.
1. You get a ransomware message.
2. You get a faux antivirus message.
3. You have got unwanted browser toolbars.
4. Your internet searches are redirected.
5. You spot frequent, random popups.
6. Your buddies get hold of social media invites from you that you failed to send.
7. Your online password isn't always working.
1. Weak Passwords
2. Remote Keyloggers
3. Phishing Emails
4. Zero-Day Vulnerability
5. Mobile Operating System Vulnerabilities
In the lovely garden, among the revelers, Shakespeare. In fact, she was seen in some parts of the hall.
The AI systems have read, analyzed, and digested the entire collective knowledge of humanity. What happens when AI has read everything?
If you want to withdraw your Coinbase account to your PayPal account, you've come to the right place. Follow these simple steps, and you'll have your money quickly.
Don't know how to make text move in CapCut? Check out this quick and easy guide that will show you how to make your text move in CapCut in no time!


